Website Security
Best Practices
Website security is a set of measures that are taken to protect a website from cyberattacks and exploitation, as well as ensuring that website data remains private and is not exposed to cybercriminals. Successful attacks can cause costly clean-up, damage the reputation of the University, and discourage visitors from coming back.
For more information on safely collecting data with online forms and data privacy, please refer to our Forms & Data Collection best practices page.
Why?
Globally, 30,000 websites are hacked daily1. Specifically, cybercriminals are looking to:
- Steal, change or destroy information, particularly your website visitors' personal information and data.
- Install malware that will spread and wreak havoc on your website visitors' devices.
- Serve up or direct your website visitors to questionable or embarrassing content.
In a nutshell, hackers are out to embarrass and degrade the reputation of respected businesses and institutions, as well as make people's lives hard and steal their money.
How?
1. Use SSL certificates and HTTPS
- SSL certificates enable encryption, transforming data into an unreadable format for anyone except the intended recipient. This allows your web pages to be served via HTTPS instead of HTTP.
- Use HSTS (HTTP Strict Transport Security) instead of simply redirecting HTTP to HTTPS.
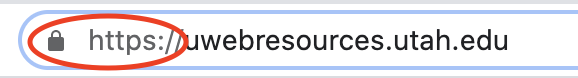
- Users can easily identify secure connections by checking the web location bar in their
browser. A URL beginning with "https://" and a padlock icon indicate that the connection
is encrypted.
- Major browsers and search engines now flag websites without SSL as "insecure," potentially eroding trust and deterring visitors.
- Please note if your website is hosted with central web teams -- UIT, UMC, or UHealth -- SSL implementation is handled automatically.
- For those not working with any of the 3 central web teams, you may request certificates through ServiceNow
2. Keep all software up to date
- Ensure your entire technology stack is up-to-date, including the operating system, web server, database server, CMS, and third-party plugins. Pay particular attention to security patches. Follow University policy Rule 4-400G, which requires monitoring vendor and third-party sources for vulnerability updates and implementing patches promptly.
- Use auto-update features whenever possible, or manually check for updates at least once a week.
- If you're managing your own instance of an open-source CMS like Drupal, WordPress, or Joomla, exercise extra vigilance. These widely-used systems are often targeted by hackers.
- Utilize the https://endoflife.date website to track end-of-life (EOL) dates and support lifecycles for various products.
- Utilize supported security protocols (eg. TLS 1.2+).
3. Manage CMS third-party plugins responsibly
If you are running your own instance of an open source content management system (CMS) such as Drupal, WordPress or Joomla, vulnerable third-party plugins are your biggest risk2. There are a number of things you can do to minimize this risk:
- Minimize your use of plugins to reduce vulnerability risk.
- Ensure you only install plugins from reputable sources after thorough research:
- Make sure the site is professionally designed and uses clear language.
- Look for a valid company name and a physical address in the footer.
- Conduct Google searches using the domain name in quotes (e.g., “example.com”), along with keywords like "exploit," "vulnerability," and "security."
- Perform similar searches with the plugin name.
- Check when the last update to the plugin was made. Avoid plugins that haven't been updated in over 6 months.
- Check the number of active installs of the plugin. Anything below around 1,000 may not be actively maintained.
- Regularly review your installed plugins to ensure they maintain good standing.
- Keep plugins up to date. Use auto-update features where available.
- Periodically clean up and delete unused plugins to minimize potential security risks.
4. Use University authentication/single sign-on (SSO)
- Adhere to University policy Rule 4-004D, which mandates the use of the Information Security Office’s (ISO) authentication services "wherever technically feasible."
- For assistance, please submit a ticket with the Identity & Access Management (IAM) team within UIT.
- When using ISO's authentication services is not technically feasible, always change default system credentials.
5. Limit access
- Consider the audience and implement role-based access controls (RBAC) to manage user permissions effectively. RBAC ensures that users are granted access based on their specific roles within the organization.
- Utilize the principle of least privilege when assigning permissions. This principle dictates that users should only have access to the systems and functions necessary to perform their job duties, and only for as long as they need it.
6. Use a website monitoring tool
- Time is critical during a website attack. Implementing a website scanner or monitoring tool enables daily threat detection, providing immediate alerts to minimize potential damage. Some advanced scanners can even automatically remove known malware.
- Regularly monitor web application logs for signs of threats and common web vulnerabilities.
7. Disable system defaults
- Replace default passwords for user accounts with strong, unique passwords.
- Disable index pages to prevent unauthorized access.
